Remember the landmark data breach in 2015?
Anthem medical data breach was the largest healthcare data breach in U.S. history! Anthem Inc. recently, in 2020, resolved its last open investigation, and according to the HIPAA journal, it paid $179.2 million to settle lawsuits and legal actions and an additional $48.2 million as a financial penalty.
According to The New York Times, about 80 million company records were hacked. The compromised information contained names, birthdays, medical I.D.s, social security numbers, street addresses, e-mail addresses, and employment information, including income data, causing fear of identity theft.
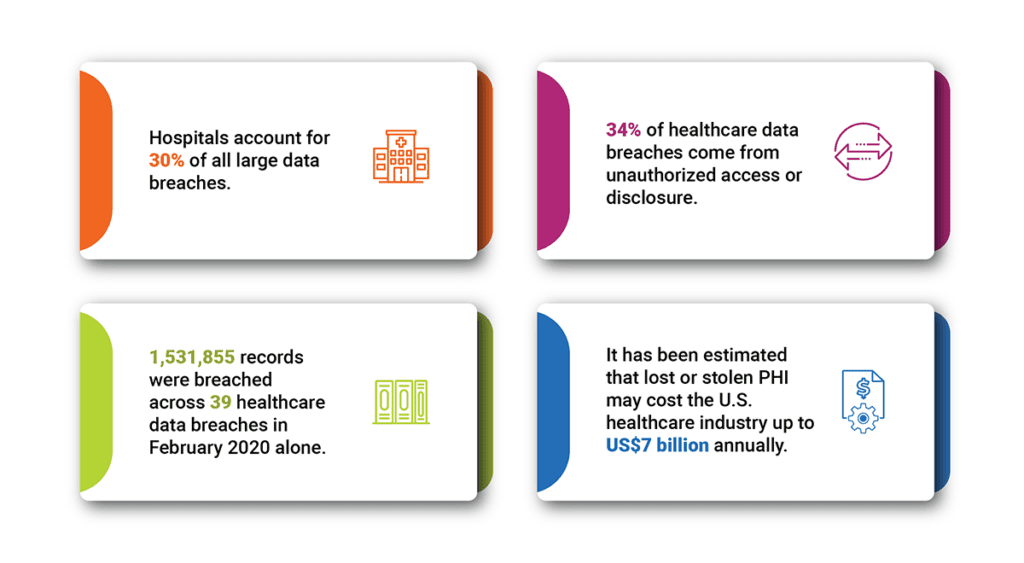
Here are some more prominent Healthcare data breaches statistics compiled by techjury
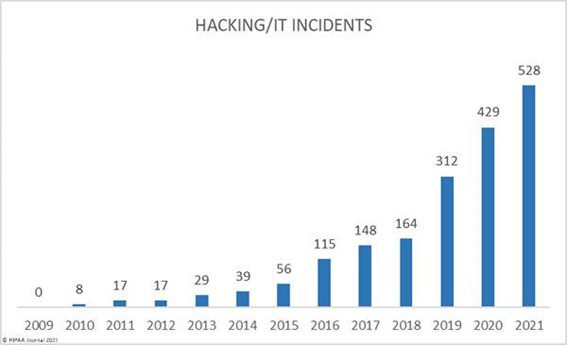
The Healthcare industry has undergone a rapid transformation over the last few years. The radical shift in healthcare operations can be seen especially after the COVID-19 pandemic. The digital shift has increased the risk of healthcare data being exposed to cybercriminals, questioning the practices used to protect health information. According to a report by HIPAA Journal, the number of hacking incidents leading to data breaches has increased recently.
PHI Sensitivity & Complications
In 2021, when hospitals and healthcare systems were still recovering from the stress caused by COVID-19, the number of healthcare data breaches was at its highest. Each day, 1,95 healthcare data breaches with 500 or more records were reported.
Healthcare data include sensitive PHI (Protected Health Information) data, and a breach can put this sensitive data at risk. Consumer PHI is an inventory of valuable, personally identifiable information, making it a treasure for cybercriminals to steal and sell. They hold the healthcare data hostage and demand a ransom from the provider or organization in question. In a 2021 FBI report, at least 148 healthcare organizations suffered ransomware attacks. It is no surprise that the healthcare industry is a vulnerable target for cybercriminals, and ransomware attacks are increasing.
How can healthcare providers secure PHI and sensitive data efficiently?
Healthcare data is growing fast as the industry adopts digitalization. Health data is generated and handled by various functions such as healthcare providers, public health organizations, insurance companies, pharmacies, patients, etc. This makes it prone to risks as multiple copies of the same data are stored at different locations, on other storage systems, and accessed by various people. Where is the control? How is the ‘what,’ ‘where,’ ‘why,’ and ‘who’ of the data monitored?
The most efficient solution for effective and efficient healthcare data management is to move it to the cloud, preferably a hybrid cloud. By consolidating this fragmented data ecosystem, the cloud will improve data security with greater consistency, uniformity, and centralization. However, moving this vast sprawl of unstructured and sensitive data to the cloud intelligently and securely requires a thoughtful, systematic, data-driven approach.
The following are some best practices that can help the healthcare industry move to the cloud and further safeguard PHI data:
Categorize hot and cold data based on metadata analytics: Classify and categorize data into hot and cold based on file ownership, time of creation, last accessed, type & size. Further, custom tagging can help categorize the data by creating custom information about the data to access it quickly and easily.
Identify PHI or sensitive data before moving to the cloud: Data analytics and pattern recognition, assisted by AI and ML, can help healthcare identify PHI or sensitive data that can put them at risk if disclosed. This can lead to greater accuracy in identifying PII/sensitive data and optimum remediation for protecting sensitive data.
Protect sensitive data from unauthorized access and misuse: After scanning and identifying the PHI and sensitive data, protect it from unauthorized access by excluding public access. With intelligent file access control, this risk of sensitive data access and misuse can be reduced.
Quarantine your sensitive data in a secure and easily accessible location: The reported sensitive data can be quickly and securely moved to a more secure and accessible storage location from the current storage. Quarantining this data can help prevent ransomware attacks while providing immediate protection.
Assess Industry Compliance (HIPAA): Healthcare providers and organizations can assess and identify data associated with regulatory requirements falling under HIPAA using context analysis. This helps with actionable data-driven insights and reports that allow data custodians to decide what data to store, how to store it, and what access and use are appropriate with the individual’s consent.
Enable audit trails: Auditing creates an immutable record of changes performed on the sensitive data files. Files can be classified and tracked utilizing blockchain technology to create an immutable audit report. The audit log creates a digital chain of custody for files with critical business information by recording every time the file is accessed or modified. Whenever an audited file is modified, the change is added to the blockchain, and you can then view a report of all audited changes for the dataset as a whole or a specific file, as needed. This can be utilized for regulatory and internal data governance.
Data Dynamics is a leading provider of enterprise data management solutions via its Unified Unstructured Data Management Platform. Currently utilized by over 25 Fortune 100 companies, the platform blends automation, AI, machine learning, and blockchain technologies, allowing organizations to use a single software platform to unlock insights, secure data, ensure compliance and governance & drive hybrid cloud data management.
Our recent collaboration with Microsoft is helping healthcare organization accelerate their cloud migration journey. Organizations can now move petabyte-scale unstructured data into Azure at ZERO cost. The migrations are 100% automated and intelligent and ensure top-of-the-line security & compliance with automatic access control and file security management.
Click here to know more about the program.
Click here to check out how Data Dynamics utilized the Azure File Migration Program to help one of the world’s seven multinational energy “supermajors” Fortune 50 companies accelerate its net zero emission goals while driving digital transformation.
Visit – www.datadynamicsinc.com. Contact us at solutions@datdyn.com or click here to book a meeting.